So, yesterday, I had to fix a friends laptop. The machine in question had your now classic situation of malware that behaved like normal antivirus software. This type of malware is beyond annoying for the simple fact that it tends to restore itself after a cleaning. Indeed, just being able to even gain access to the software to clean said infection can sometimes be near impossible, as most malware of this type is programmed to block virtually every application a user tries to run, including virtually any form of antivirus a user might use.
The machine in question is a Toshiba Satellite running 32bit Windows 7. UAC was fully active on the machine, so, I questioned naturally how the software actually made it onto the system. User error, of course… but this isn’t a blame game. Stuff happens, and the situation at hand was obvious: I would have a battle ahead of me.
So, naturally, my first action was to see what actually would run on the system… which of course, was virtually nothing. That is, until the fake antivirus made a little mistake: it would try to run more admin-level code, which would bring up a UAC prompt. Saying no to this would kill the software, and leave the system running in a mostly usable state. The processor, however, was slammed 100% with a “Com” process, which was something related to the antivirus… probably a batch code to “fake” system instability. Using the now-available task manager (which was originally unavailable while the fake AV was running) killed that off quickly enough, and left me in a good state to clean the system.
So, I ran Avira.. it detected the virus, and appeared to clean it. I rebooted the system… and the virus was still there. Avira was unable to properly clean the system. I planned for as much, but of course wanted to try the most simple option first.
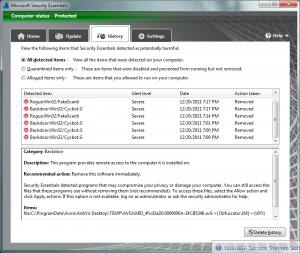
I decided to, after once again killing off the malware, download and run Microsoft Security Essentials. I was going to change the system out to this antivirus anyway, so it was a way to complete 2 tasks at once.
After installing MSE, and letting the definition update, I let it run. This was actually my first run of MSE on a system that was known to be infected, so this was a chance to actually see the program in action, and to judge its effectiveness on cleaning a system. It quickly detected the infected files and painlessly cleaned them. After rebooting, I noticed that the malware did not load up with the system: it seemed clean!
I ran another scan of the system. Nothing detected. I checked the system processes; everything looked good. I had beaten the virus. Normally, the best option to be rid of such malware is to simply do a system restore, but in this case, I was able to clean the system without any permanent damage being done. Obviously, I was very happy with the end result, and I hope the owner of the laptop will be as well.